Consider A One Way Authentication Technique Based On Asymmetric Encryption 13+ Pages Summary [1.6mb] - Updated 2021
29+ pages consider a one way authentication technique based on asymmetric encryption 800kb. IDA B -- A. Consider a one-way authentication technique based on asymmetric encryption. IDA EPUBRA BS A. Read also based and learn more manual guide in consider a one way authentication technique based on asymmetric encryption Consider a one-way authentication technique based on asymmetric encryption.
IDA B S A. IDA B S A.
S Mdpi 2076 3417 11 16 7339 Pdf
| Title: S Mdpi 2076 3417 11 16 7339 Pdf |
| Format: PDF |
| Number of Pages: 348 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: June 2018 |
| File Size: 3mb |
| Read S Mdpi 2076 3417 11 16 7339 Pdf |
 |
R1 A S B.

Consider a one way authentication technique based on asymmetric encryption A B from IFT 302 at Arizona State University. View certificate_kerberostxt from DF df at National Film School of Denmark. E PR a R1 a. What type of attack is this protocol susceptible to. Modify the protocol to provide bidirectional authentication. EPUa R2 A S B.

Chapter 2 Cryptographic Tools Ppt Download
| Title: Chapter 2 Cryptographic Tools Ppt Download |
| Format: eBook |
| Number of Pages: 186 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: April 2018 |
| File Size: 1.4mb |
| Read Chapter 2 Cryptographic Tools Ppt Download |
 |

Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram
| Title: Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
| Format: PDF |
| Number of Pages: 189 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: August 2020 |
| File Size: 810kb |
| Read Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
 |

Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram
| Title: Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
| Format: eBook |
| Number of Pages: 163 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: August 2018 |
| File Size: 5mb |
| Read Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
 |
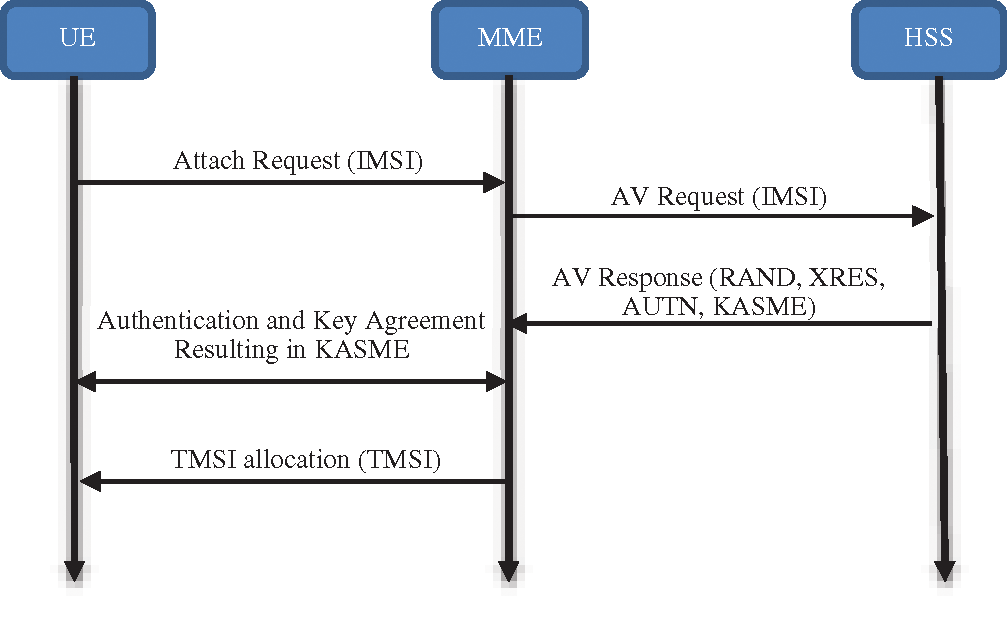
Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4
| Title: Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4 |
| Format: PDF |
| Number of Pages: 297 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: January 2018 |
| File Size: 3.4mb |
| Read Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4 |
 |
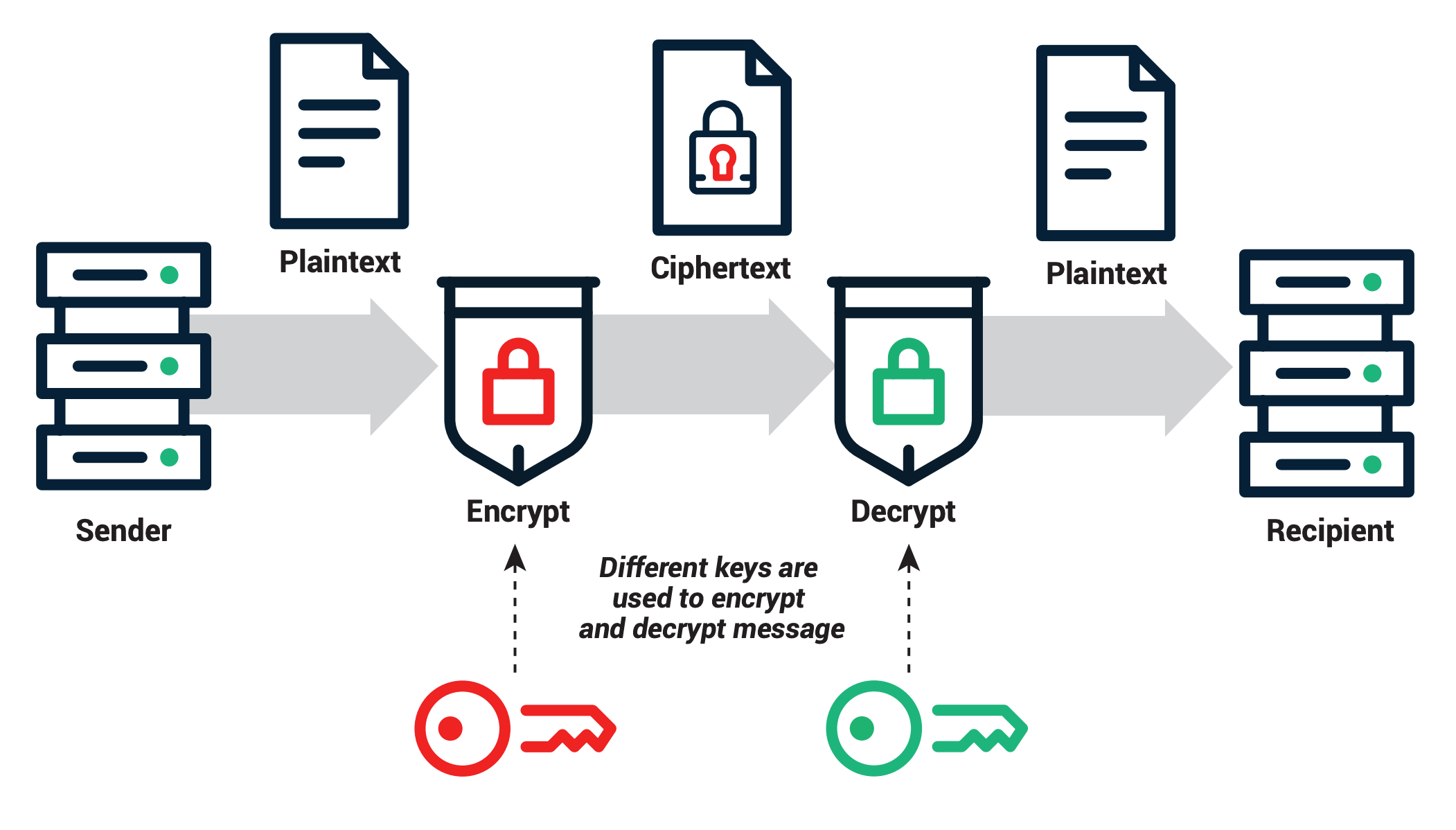
Public Key Cryptography Explained Sectigo Official
| Title: Public Key Cryptography Explained Sectigo Official |
| Format: ePub Book |
| Number of Pages: 235 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: May 2017 |
| File Size: 1.9mb |
| Read Public Key Cryptography Explained Sectigo Official |
 |

What Is Symmetric Key Cryptography Encryption Security Wiki
| Title: What Is Symmetric Key Cryptography Encryption Security Wiki |
| Format: ePub Book |
| Number of Pages: 280 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: February 2021 |
| File Size: 1.6mb |
| Read What Is Symmetric Key Cryptography Encryption Security Wiki |
 |

Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4
| Title: Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4 |
| Format: PDF |
| Number of Pages: 161 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: May 2021 |
| File Size: 3.4mb |
| Read Puter Systems Science Engineering Doi 10 32604 Csse 2021 015593 Images Article Pseudonym Mutable Based Privacy For 5g User Identity Rashid A Saeed 1 Mamoon M Saeed2 3 Rania A Mokhtar1 Hesham Alhumyani1 And S Abdel Khalek4 |
 |

3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram
| Title: 3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram |
| Format: ePub Book |
| Number of Pages: 261 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: March 2017 |
| File Size: 5mb |
| Read 3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram |
 |
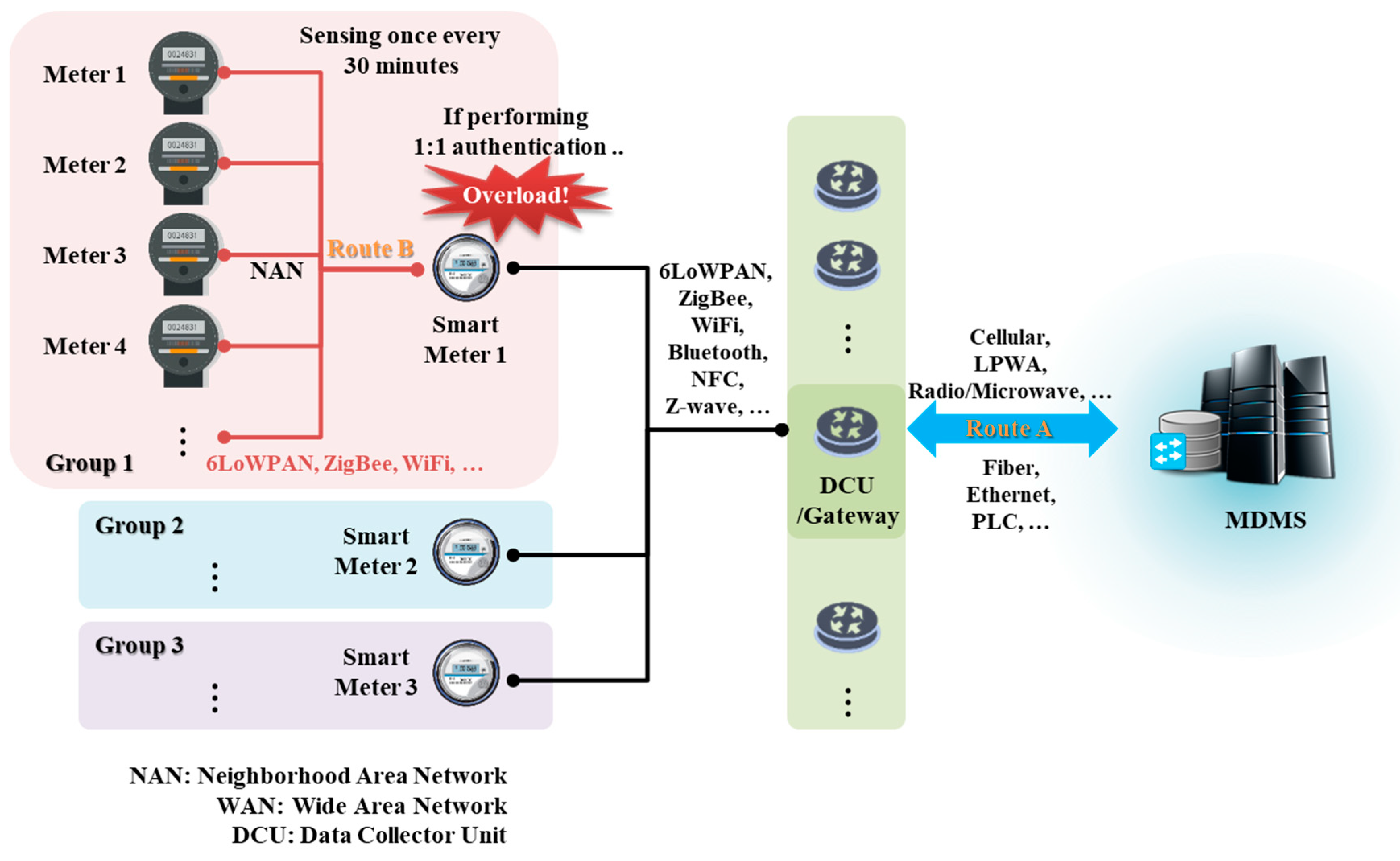
Sensors Free Full Text Dynamic Group Authentication And Key Exchange Scheme Based On Threshold Secret Sharing For Iot Smart Metering Environments Html
| Title: Sensors Free Full Text Dynamic Group Authentication And Key Exchange Scheme Based On Threshold Secret Sharing For Iot Smart Metering Environments Html |
| Format: eBook |
| Number of Pages: 135 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: January 2017 |
| File Size: 3mb |
| Read Sensors Free Full Text Dynamic Group Authentication And Key Exchange Scheme Based On Threshold Secret Sharing For Iot Smart Metering Environments Html |
 |

Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram
| Title: Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
| Format: eBook |
| Number of Pages: 168 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: July 2019 |
| File Size: 1.2mb |
| Read Gdoi Phase 1 Authentication Based On Isakmp Exchanges The Indicates Download Scientific Diagram |
 |
3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram
| Title: 3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram |
| Format: eBook |
| Number of Pages: 180 pages Consider A One Way Authentication Technique Based On Asymmetric Encryption |
| Publication Date: February 2021 |
| File Size: 2.2mb |
| Read 3 Phase 1 Authentication With A Pre Shared Key Main Mode Download Scientific Diagram |
 |
View certificate_kerberostxt from DF df at National Film School of Denmark. EPUa R2 A S B. Modify the protocol to provide bidirectional authentication.
Here is all you have to to read about consider a one way authentication technique based on asymmetric encryption E PR a R1 a. What type of attack is this protocol susceptible to. 2 question Consider a one-way authentication technique based on asymmetric encryption. Chapter 2 cryptographic tools ppt download 3 phase 1 authentication with a pre shared key main mode download scientific diagram s mdpi 2076 3417 11 16 7339 pdf gdoi phase 1 authentication based on isakmp exchanges the indicates download scientific diagram public key cryptography explained sectigo official what is symmetric key cryptography encryption security wiki EPRa R1 Explain the protocol.


No comments:
Post a Comment